Table of Contents
In the modern digital economy, data is the most valuable currency. For small to medium-sized enterprises (SMEs), this reality is a double-edged sword. While digital transformation allows small teams to compete on a global scale, it also places them directly in the crosshairs of sophisticated cybercriminal syndicates. At Cinute Infomedia, we have seen firsthand how a single vulnerability can jeopardize years of hard work.
The misconception that "we are too small to be a target" is the single greatest security risk a business can face. In 2024, cyberattacks are largely automated; bots don't care about your revenue—they care about your vulnerabilities. This guide provides an exhaustive roadmap to securing your digital perimeter.
1. The Anatomy of the Modern Threat Landscape
Before implementing tools, business owners must understand the "Who, How, and Why" of modern cybercrime. The 2024 landscape is dominated by decentralized hacking groups utilizing AI to scale their operations.
The Phishing Evolution: Beyond Suspicious Emails
Phishing remains the #1 entry point for breaches. However, the days of poorly spelled emails from "foreign princes" are over. Today, attackers use Generative AI to craft perfect, personalized messages that mimic the tone of your vendors or even your CEO (a tactic known as Business Email Compromise or BEC).
The Ransomware Pandemic
Ransomware is no longer just about locking files; it is now "Triple Extortion." Attackers encrypt your data, steal it to threaten public release, and then contact your clients to inform them of the breach. This creates a reputational crisis that most small businesses cannot survive.
Why 60% of SMEs Fail Post-Attack
Statistics show that 60% of small businesses go out of business within six months of a cyberattack. The reason isn't just the ransom-it’s the downtime, the legal fees, the loss of customer trust, and the inevitable regulatory fines.
Expert Insight: Security starts at the code level. If your current website is outdated, you are leaving the front door unlocked. Consider our specialized Web Development Solutions to ensure your digital storefront is built on a secure, modern framework.

2. Building the Human Firewall: Employee Training & Culture
Technology can only protect you so far. If an employee clicks a malicious link, the most expensive firewall in the world becomes irrelevant.
Security Awareness as a Monthly Ritual
Annual training is ineffective. Cyber threats evolve weekly. Implement a continuous learning culture where employees are tested with "safe" phishing simulations. These exercises turn your staff from a liability into your strongest line of defense.
The "Clean Desk" and "Clean Device" Policy
In an era of remote work, the line between personal and professional devices has blurred. Establishing clear policies on how business data is handled on home Wi-Fi networks is critical for maintaining a "Zero Trust" environment.
Identifying Social Engineering
Train your team to verify "urgent" requests. If a vendor suddenly changes their bank details via email, your policy should mandate a voice-call verification before any funds are moved.
3. Strong Authentication: The End of the Simple Password
Passwords are the weakest link in the security chain. In 2024, "Password123" is cracked in milliseconds by brute-force bots.
Implementing Multi-Factor Authentication (MFA)
MFA is the single most effective deterrent against account takeover. By requiring a second form of verification-such as a push notification or a hardware key-you block 99.9% of automated attacks.
The Role of Enterprise Password Managers
Employees should never know their own passwords. By using tools like LastPass or Dashlane for Business, your organization can enforce 20-character complex strings that are stored in an encrypted vault, ensuring that a breach of one service doesn't lead to a total system collapse.
Biometric Integration
Where possible, leverage "Passkeys" and biometrics (FaceID/Fingerprint). These are significantly harder to intercept than traditional SMS-based codes, which can be diverted via SIM-swapping attacks.
Digital Transformation Tip: Managing internal access is just as important as blocking external threats. Explore how our Software Development Services can help you build custom internal tools with built-in role-based access control (RBAC).

4. The 3-2-1 Backup Strategy: Your Insurance Policy
If an attack succeeds, your backup is the only thing that prevents you from paying a ransom. However, many businesses realize too late that their backups were also encrypted by the attacker.
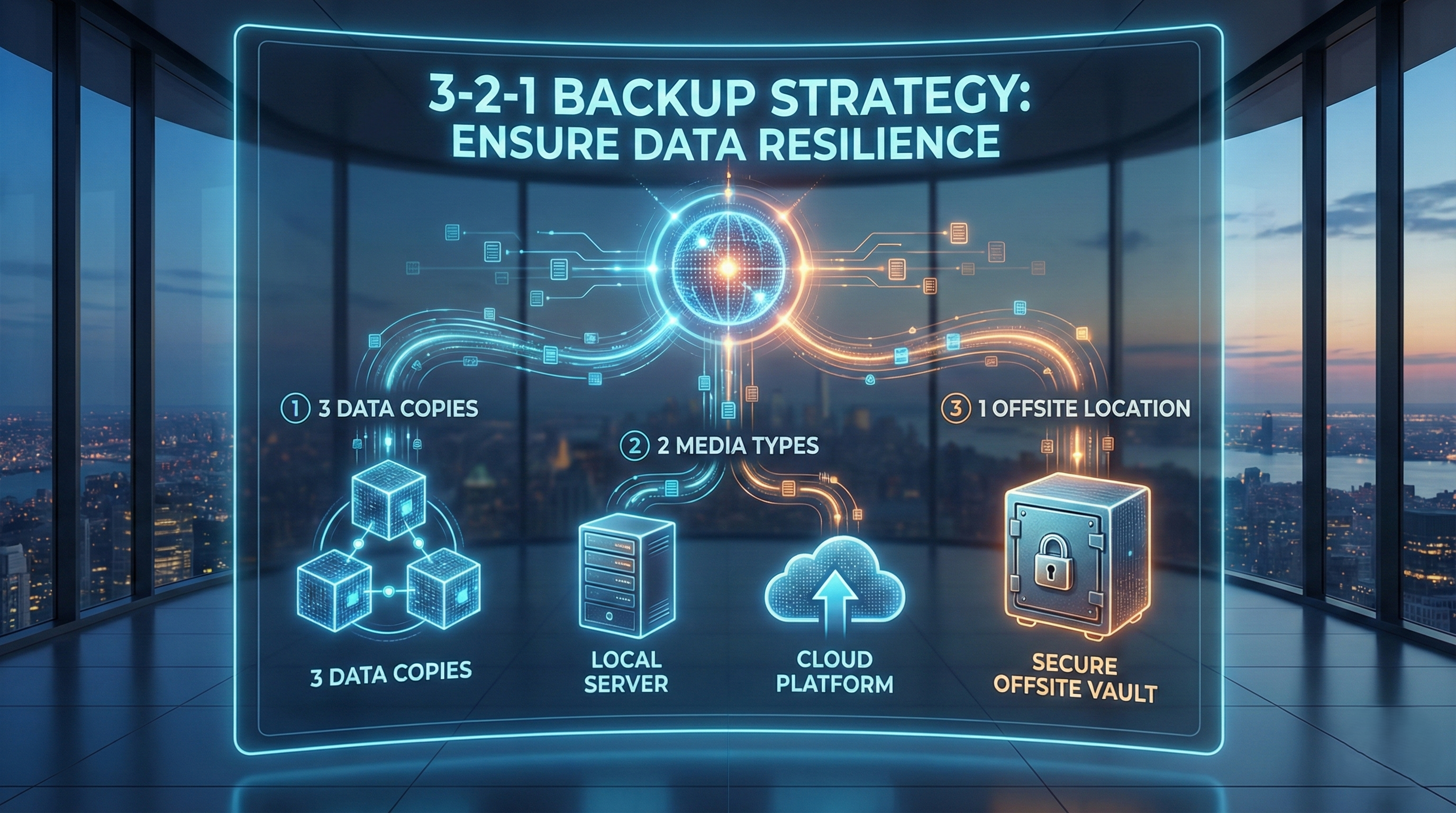
The 3-2-1 Rule Explained
- 3 Copies of Data: The original and two backups.
- 2 Different Storage Types: For example, one on a local NAS and one in the cloud.
- 1 Offsite/Immutable Backup: One copy must be physically or logically disconnected from your main network (Air-gapped).
Automated Integrity Checks
A backup is only good if it actually works. Automated scripts should not only move the data but also verify its integrity. Below is a sample concept of a secure backup routine:
Bash
#!/bin/bash # CINUTE INFOMEDIA - Secure Daily Backup Routine BACKUP_DIR="/secure-vault/$(date +%Y%m%d)" mkdir -p $BACKUP_DIR # Encrypt and Compress tar -czf - /var/www/data | openssl enc -aes-256-cbc -salt -out $BACKUP_DIR/data_encrypted.tar.gz echo "Backup and AES-256 Encryption completed: $BACKUP_DIR"
Business Continuity Planning (BCP)
Having data is one thing; knowing how to restore it under pressure is another. Conduct a "Fire Drill" twice a year where you attempt to restore your entire business operation from backups to measure your Recovery Time Objective (RTO).
5. Mobile & Endpoint Security: Securing the "Edge"
As work becomes increasingly mobile, the "perimeter" of your business is now wherever your employees are holding their phones.
Mobile Device Management (MDM)
If an employee loses their phone, can you wipe the business data remotely? MDM solutions allow you to separate personal data from business data, ensuring that "Bring Your Own Device" (BYOD) policies don't become a security nightmare.
Endpoint Detection and Response (EDR)
Traditional antivirus is reactive. EDR is proactive. It monitors the behavior of every laptop and phone in your network, using AI to spot anomalies—like a computer suddenly trying to encrypt 1,000 files a minute—and shuts the process down before the damage spreads.
SEO Strategy Note: A secure app is a successful app. If you are launching a mobile product, check our Mobile App Development Services to see how we integrate "Security by Design" into every mobile interface.
6. Network Defenses and Secure Hosting
Your website is the face of your business, but it is also a public-facing portal into your digital life.
SSL, WAF, and DDoS Protection
Every site must have an SSL certificate, but 2024 requires a Web Application Firewall (WAF). A WAF filters out malicious traffic before it even reaches your server, blocking SQL injection and Cross-Site Scripting (XSS) attacks.
The Danger of Shared Hosting
Many small businesses use cheap, shared hosting. If another site on that server is hacked, the attacker can often "jump" to your site. High-performance businesses should opt for managed, isolated environments.
Infrastructure Tip: Speed and security go hand-in-hand. Our UI/UX Design Services prioritize clean, secure code that reduces vulnerabilities while maximizing user engagement.

7. Compliance and the Legal Imperative
Cybersecurity isn't just a technical issue; it's a legal one. Depending on your industry and location, you may be subject to GDPR, CCPA, or HIPAA.
Data Privacy as a Marketing Tool
In an age of data leaks, being able to tell your customers "Your data is encrypted and we are SOC2 compliant" is a massive competitive advantage. It builds a level of trust that your unoptimized competitors cannot match.
Incident Response Plans (IRP)
Who do you call when you get hacked? Your lawyer? Your IT provider? The authorities? An IRP is a physical document that lists the roles and responsibilities of every team member during a crisis.
Marketing Insight: Security is a major part of your brand authority. Use our Digital Marketing Services to communicate your commitment to safety and privacy to your target audience.

Conclusion: Turning Vulnerability into Strength
In 2024, cybersecurity is no longer an IT expense-it is a foundational element of business strategy. Small businesses that ignore these practices aren't just taking a risk; they are operating on borrowed time. By implementing MFA, enforcing the 3-2-1 backup rule, and fostering a culture of awareness, you create a resilient organization that can withstand the storms of the modern internet.
At Cinute Infomedia, we don't just build websites and apps; we build secure digital futures. Protecting your reputation and your customers is a journey, and it begins with the first step of securing your infrastructure today.
Related Articles
Recover 30% of Lost Sales With a Smart Cart Bot
Most stores lose two-thirds of their carts before checkout. Learn how a smart cart recovery bot quietly wins those orders back often 30% or more.
How to Use Speed Optimization Plugins the Right Way
A slow site quietly drains your leads every day. Learn how to use speed optimization plugins the right way and turn load time into revenue

How to Run an Enterprise App Security Audit Without Downtime
Most teams delay security audits, fearing downtime and lost revenue. Here's how to run a complete enterprise app security audit while your app stays fully live
